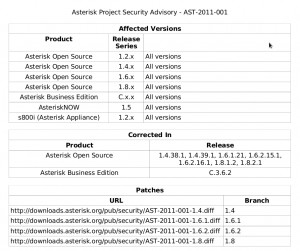
Sicurezza: AST-2011-001 – Stack buffer overflow in SIP channel driver
Ecco un estratto del documento sulla sicurezza AST-2011-001:
Description When forming an outgoing SIP request while in pedantic mode, a stack buffer can
be made to overflow if supplied with carefully crafted caller ID information. This
vulnerability also affects the URIENCODE dialplan function and in some versions
of asterisk, the AGI dialplan application as well. The ast_uri_encode function does
not properly respect the size of its output buffer and can write past the end of it
when encoding URIs.
Resolution The size of the output buffer passed to the ast_uri_encode function is now
properly respected.
In asterisk versions not containing the fix for this issue, limiting strings originating
from remote sources that will be URI encoded to a length of 40 characters will
protect against this vulnerability.
exten => s,1,Set(CALLERID(num)=${CALLERID(num):0:40})
exten => s,n,Set(CALLERID(name)=${CALLERID(name):0:40})
exten => s,n,Dial(SIP/channel)
The CALLERID(num) and CALLERID(name) channel values, and any strings passed
to the URIENCODE dialplan function should be limited in this manner.

Leave a comment
Devi essere connesso per inviare un commento.